Artificial Intelligence
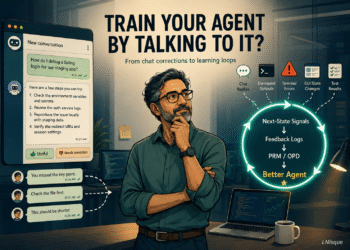
Train Your Agent by Talking to It? My First Attempt to Bring OpenClaw-RL into BizClaw
A practical reflection on OpenClaw-RL, BizClaw/NanoClaw, and why I started with Telegram feedback buttons before attempting full RL or…Continue reading...
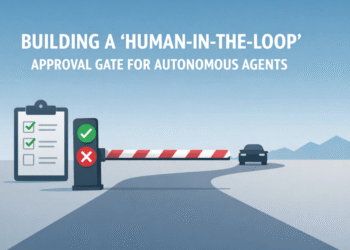
Read moreBuilding a ‘Human-in-the-Loop’ Approval Gate for Autonomous Agents
In this article, you will learn how to implement state-managed interruptions in LangGraph so an agent workflow can pause for...
Read moreU.S. Officials Want Early Access to Advanced AI, and the Big Companies Have Agreed
Microsoft, Google DeepMind and Elon Musk’s xAI have offered to let the U.S. government access new AI models ahead of...
Read moreA blueprint for using AI to strengthen democracy
Technology has always shaped the way citizens interact with information. But a new problem will soon arise in the form...
Read moreIdentify content made with Google’s AI tools
Advances in generative AI are making it possible for people to create content in entirely new ways — from text...
Read moreI Tried Four Smarter Ways to Select Positions in GCG.
A weekend-nights-and-GPUs deep dive into adversarial attacks against LLMs, where the most interesting finding was the one I didn’t expect.Continue...
Read more7 Machine Learning Trends to Watch in 2026
In this article, you will learn how machine learning is evolving in 2026 from prediction-focused systems into deeply integrated, action-oriented...
Read moreWhite House Weighs AI Checks Before Public Release, Silicon Valley Warned
President Donald Trump’s White House is contemplating whether the US government should be allowed to screen the most powerful AI...
Read moreCyber-Insecurity in the AI Era
Cybersecurity was already under strain before AI entered the stack. Now, as AI expands the attack surface and adds new...
Read moreGemini as a universal AI assistant
Over the last decade, we’ve laid a lot of the foundations for the modern AI era, from pioneering the Transformer...
Read more